
The Tonie figurines are used to control the Toniebox. By placing a Tonie figurine on top of the Toniebox, the Box will read the rfid chip within the figurine and start playing the corresponding story.
This article will go into the depth of the rfid chip within the Tonie figurine.
Structure of Article
- position of chip
- rfid chip type
- memory structure
- UID structure
- How to read the Tonie rfid chip
- privacy mode
- disabling privacy mode
- password for privacy mode
- alternative unlock methode
- needed Hardware
- Proxmark3
- command samples
- ChameleonMini
- Arduino + PN5180
- CR95HF dev board with python script
- Proxmark3
- privacy mode
- Structure of rfid chip content
- usage within the Tonie universe
- structure around the Tonie universe
- what happens within the toniebox
- SD card content
position of chip
In each figurine there are two hallow spaces kept free during production.
One is located right at the bottom of the figurine to hold a small magnet. This attaches the figurine to the Toniebox to prevent it to fall off.
The other one is located at about 20mm higher location where the small rfid chip is located at. This must be a sweet spot of the Toniebox RF reader field.
A lot of figurines are made of two parts which are glued together after the chip is inserted into the middle section.

The chip sits just beneath the neck.
rfid chip type
The specific chip that is used within the Tonie figurine is an ICODE SLIX-L chip produced by NXP Semiconductors wich operates within the iso15693 Standard.

This chip works with an antenna frequency of 13,56 MHz but is not compatible with the widely known standard iso14443 nor the iso14443 rfid readers used for MiFare RFID chips.
The specific chip used by Boxine GmbH for the Tonie figurine looks a bit like an glas transponder that is used for tagging of animals but without the glas tube. According to the founders of the Toniebox this chip is produced in India.
memory structure of SLIX-L
The SLIX-L chip has a 8 Byte long UID and a 32 Byte long memory wich is structured in 8 Blocks of 4 Byte each.
UID structure
The first four Bytes of each Tonie rfid chip UID (unique identifier) are the same (as of now).
E0 04 03 50 xx xx xx xx
E0 identifies the iso15693 standard
04 identifies the chip manufacturer (= NXP Semiconductors)
03 identifies the chip type (= SLIX-L)
50 part of the serial number
xx 4 Byte long Tonie identifier
How to read Tonie rfid chip
Even by using the correct rfid reader for the iso15693 standard, or using devices like the proxmark3, the Tonie figurine stays silent when standard commands are used to communicate with the chip.
With the SLIX2 class rfid chips, where the SLIX-L belongs to, NXP Semiconductors introduced some security features.
These features can be controlled, activated and deactivated by custom commands and prior set passwords.
More details can be found within the SLIX-L data sheet at 9.4.3, or within the SLIX2 data sheet at 9.5.3.
privacy mode
One of these features is the privacy mode. If this is enabled the chip will only respond to two custom commands. With all others the chip will remain silent.
disabling privacy mode of Tonie figurine
To disable the privacy mode and therefore opening the Tonie figurine to the standard rfid commands for further reading of the UID and the chip memory content a few actions needs to be taken.
At first a Password is needed. This is set within the production process by the OEM and is set by Boxine GmbH.
At second with the custom command GET RANDOM NUMBER (9.4.3.1) a two Byte long random number generated by the chip itself can be retrieved.
The passwords first two bytes and the passwords second two bytes need to be XORed with the two byte long random number and set back together to a 4 byte long XORed password.
At third with the custom command SET PASSWORD (9.4.3.2) the XORed password is send to the rfid chip and will disable the privacy mode.
password for privacy mode
The password can be retrieved by snooping the communication between the Toniebox and the Tonie figurine while the Tonie is placed on top of the Toniebox.
Snooping can be done with the proxmark3.
Further information on the proxmark3 can be found within the proxmark3 forum.
In addition there are some other forums where the password is posted, so that the snooping work does not be done again.
(I will not post it!)
alternative unlock methode
When the Tonie figurine is placed on top of the Toniebox, the Box itself needs to disable the provacy mode to get the UID and the memory contenct. After these information are read, the Toniebox will enable the privacy mode again. This takes place within under a second.
I figured out, that with the „knock method“, you are able to get the Tonie figurine off the Toniebox before it activates the privacy mode.
To use the „knock method“ you need to hold the Tonie in your hand and knock the stand side (side with magnet) onto the Box reader surface and lift the Tonie immediately. It should just be a knock and not a place and lift off the Tonie.
With a bit of practice you can disable the privacy mode without knowing the password and go further with standard iso15693 reader to read the chip UID and the content of the memory.
Needed Hardware for reading
After the privacy mode of the SLIX-L chip is successfully disabled you can start to read the UID and the memory content.
To read the rfid chip of a Tonie figurine with a disabled privacy mode every rfid reader that is able to read iso15693 standard chips can be used.
I will show show three rfid readers that are my first choice to go with.
proxmark3
The proxmark3 is a universal rfid reader for all kind of rfid standards in low frequency (125kHz) and high frequency (13,56MHz) mode.
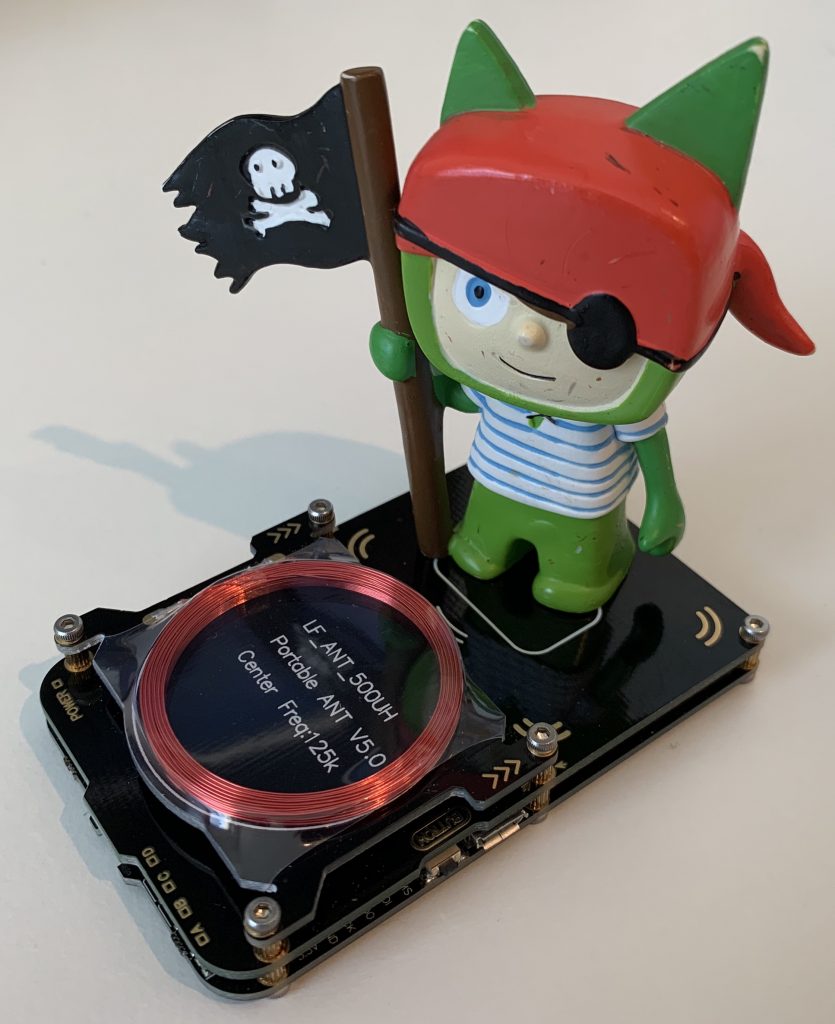
It is so versatile that it enables sniffing, reading and cloning of rfid tags and is capable of reading, writing, and emulating many of the currently available rfid tags of multiple standards (e.g. iso14443, iso15693, ICODE ,MiFare , HID iCLASS , Legic, 125 kHz, etc.).
You can get the proxmark3 easy here. (Affiliate link).
To work with the proxmark3 you can either use a windows based GUI, or the most common way is the terminal window.
You can find detailed information regarding setup and firmware upgrades of the proxmark3 within the following Repos at GitHub:
- RRG / Iceman Repo (RfidResearchGroup) – LINK
- Official Proxmark3 Repo – LINK
- universal Windows GUI by burma69 – LINK
some Command samples to use with Tonies:
RANDOM NUMBER
hf 15 cmd raw -c -2 02 b2 04
The two Byte long RANDOM NUMBER is needed to generate the XORed password to disable the PRIVACY MODE with the SET PASSWORD command.
SET PASSWORD disable PRIVACY MODE
hf 15 cmd raw -c -2 02 b3 04 04 xxxxxxxx
The xxxxxxxx represents the 4 Byte long XORed password. The passwords first two bytes and the passwords second two bytes need to be XORed with the two byte long random number and set back together to a 4 byte long XORed password.
WRITE PASSWORD for PRIVACY MODE
hf 15 cmd raw -c -2 22 b4 04 04 xxxxxxxxxxxxxxxx yyyyyyyy
This command will change the password for the PRIVACY MODE. For the xxxxxxxxxxxxxxxx the 8 Byte long UID needs to be inserted in reverse order (LSB). The yyyyyyyy represents the 4 Byte long NEW password.
This command only works if the SET PASSWORD command was executed successfully right before.
(Would not recommend to use this with an original Tonie figurine.)
DUMP RFID chip
dumps UID and hole memory of rfid chip (Tonie)
hf 15 dump
This command will dump the hole information and contend of the rfid chip / Tonie figurine.
The interesting part is the 8 Byte long UID and the 32 Byte long memory content.
ChameleonMini
The ChameleonMini is a freely programmable, portable tool for ISO14443 / ISO15693 / NFC security analysis that can emulate & clone contactless cards, read RFID tags and sniff/log RF data.

The ChameleonMini can not only be used to read Tonie figurines or sniff / snoop the communication between the Tonie figurine and the Toniebox to receive the password for PRIVACY MODE, it can simulate the Tonie rfid chip as well (more to this in another post).
There are different versions of the boards available. The original ChameleonMini by Kasper & Oswald is available as „ChameleonMini RevG“ Model. Two other models are available as „ChameleonMini RevE reebooted“ and as of Jan. 2019 the new Model „ChameleonMini RevG rebooted“ and „ChameleonTiny“. These are developed by Iceman and Proxgrind.
Most of the boards sold by the usual chinese online warehouses are the „ChameleonMini RevE rebooted“ Versions.
You can buy the ChameleonMini here.
To configure the ChameleonMini, Iceman build a nice Windows based GUI. You can find it in his Git. (LINK)
You can find detailed information regarding setup and firmware upgrades of the ChameleonMini within the following Repos at GitHub:
If you like to flash the ChameleonMini within windows, then you can find here more information on that. (LINK)
Arduino with PN5180 rfid reader
My favorite toy for tinkering with rfid chips is my very own dev board with an ESP8266 and an PN5180 rfid reader. In addition I have some buttons and other components on the board like a small I2C display. With this setup I am free for everything that needs to be done to an rfid chip or a Tonie in particular.
I can programm sequences of commands, save some read information in my SPIFF for further analysis later on, etc.
It can be battery operated as well.
A good start into this is the PN5180 library by Andreas Trappmann that just got an update through trueddy for iso14443 support. That means this board is feasible to work with iso14443 and iso15693 cards.
You can find the ATrappmann Library for the PN5180 here. – LINK
Within this library you will find an example which is ready to disable the PRIVACY MODE and read further information from the rfid chip. But again: The password for disbaling the PRIVACY MODE is not included.
CR95HF dev board with python script
Frederico Cerutti (ceres-c) showed at the 36C3 conferenc some Toniebox hacking. (More on this in another post.)
Part of it was to read Tonie rfid tags with a CR95HF rfid dev-board and a python script. The script disables the PRIVACY MODE and reads the UID of the Tonie rfid chip.
(Password to disable the PRIVACY MODE is not included!)
You can find the script here – LINK
You can buy the „STMicroelectronics DevBoard M24LR04E) here – (Affiliate link)
Structure of rfid chip content
Like mentioned above the chip memory structure consists of an 8 Byte long UID and a 32 Byte long memory wich is separated in 8 Blocks with 4 Bytes each.
The first 4 Bytes of the UID are always E0 01 03 50 as of now.
The last 4 Bytes is a random number according to the iso15693 standard.
The 32 Byte long memory did not show any structure to us so far. Actually I think that it might be a validation value of the UID like an SHA or a long verification string that is stored within the Tonie cloud, to verify the Tonie itself.
If you have any further information about this, please let me know.
usage withgin the Tonie universum
The structure of the systems within the Tonie universe is well thought through. I can tell you that Boxine and their staff did a really good job in designing the whole platform of the Tonie universe.
Structure of the Tonie universe
As I explained before, there are no known information within a Tonie that gives a direct hint about the audio book that it is attached to. Within the production in Tunisia where the figurines are produced (in a plant that produces the well known „Schleich Figuren“ as well), the rfid chip (which is produced in India) is placed into the figurine. In addition the information about the figurine and the UID of the chip is saved within the Boxine database. This is where the information comes together.
Every time a figurine is placed on top of a Toniebox, the box will verify wether it knows already which story belongs to the figurine (to the UID) or it will ask the Tonie Cloud Server which will transfer the correct audio file to the Toniebox which can than be played.
What happens within the Toniebox
Within the Toniebox there is a MicroSD Card installed (as far as I know these are all 4 GB large).
Everytime a figurine is placed on top of the toniebox the following steps are performed:
- disabling the PRIVACY MODE
- read the 8 Byte long UID
- read the 32 Byte long memory content
- enable the PRIVACY MODE
- check wether a directory with a name of the last 4 Byte of the UID exists.
- check wether a file with a name of the first 4 Byte of the UID exists.
- If this directory and the file exists, it is verifying the header information within the file.
The Audio file is made of two parts. The first part is an information header (e.g. chapter marks) and the second part is an ogg opus audio file.
It checks wether the Audio-ID within the header is the same within the OGG audio file. And it verifies if the length value stored within the header fits the audio file.
If these checks fail it will delete the existing file and directory. - If these checks are passed, it will start playing the audio file
- If the directory is missing, it will start communicating with the Tonie Cloud Server and will send the UID and the memory content of the rfid chip of the Tonie figurine to the Server.
- The server is verifying the UID and memory content within its database and sends in return the needed file.
- While the file is transferred it is already being played. During this the file is stored within a TEMP directory. After the transfer of the file is finished it is stored in an own directory within the CONTENT directory.
The name of the file is build out of the first 4 Bytes of the UID and the directory name consists of the last 4 Bytes of the UID written in LSB order (Byte order reversed). - While the audio is playing the box checks on a regular base with the custom command for the RANDOM NUMBER in addressed mode wether this specific Tonie is still present. Addressed mode means that it is just asking for an rfid chip with a specific UID. When this tag is not answering the box will stop the audio.
Some detailed information regarding the structure of the audio file including detailed header explanation and OGG structure walk through will follow in another blog post..
SD-Card content
The SD card ist structured into to following directories
CONTENT
all directories and files for known Tonie figurines are stored in this directory..
WITHIN the CONTENT directory:
each Tonie figurine has their own directory. The name is build out of the last 4 Bytes of the UID of the rfid chip within the Tonie.
In every directory there is one file named after the first 4 Bytes of the Tonie rfid chip UID. Because these are all the same (as of now), all files are named the same.
In addition there is one directory „00000001“ and one directory „00000000“ within the CONTENT directory as well. In these directories are the language files stored. These are the spoken animal error messages in german and in english.
In some cases there are two more files within the root of the sd card.
initsd.crc – a file that is created by initializing of the sd card and the standard structure.
PM2.LOG – this looks like a log file. No further information are available right now.
If you like to mention some improvements or hints which I should add to the content or just write it the right way, please let me know.
Either within the comment section or via eMail.
Alright, knock method…
Does it work with any iphone and nfc tag manager?
I dont get anything and i an knocking like crazy, slow/fast,sideways.
Hallo Alex,
Yes it does actually work.
You just have to be really quick. It is just a little touch and a quick release. Thats why I called it knock methode back when I found it out because it is just a little quick knock with the tag on the box.
After that you can use NFCmanager with your iPhone to read the UID.
Regards,
Gambrius
Hi,
Is it possible to save custom language files? So box can speak another language?
Hallo Kamil,
The language files are stored on the SD card (within the 000000 and the 000001 directory). Right now there are only german and english language files existing.
With the Tool Teddy by Team RevvoX it should not be a problem to exchange every single file with an own creation.
If you will do further work on own language files, please let me know. I would like to cover the information within this Blog.
Regards,
Gambrius
O that is great. Thank you very much for the information. I will keep you updated – I should receive Tonibox in few days.
I wanted to double check – SL2S2002 (SLIX) won’t work, it must be SL2S5002 (SLIX-L)?
Hallo Kamil,
Correct. It MUST be an SLIX-L.
Regards,
Gambrius
Hi.
First of all: Thanks for your Input! Really good advices.
And now my question: copying a tonie-figure is as I understand Just by the UID. Is there a possibility to Change the UID of a SLIX-L Tag. Can proxmark3 copy a whole Tag incl. UID?
Is it possible to use another iso15693 Tag With variable UID but larger Space?
Thanks in advance!
Hallo Babidu,
The Toniebox is not just reading the UID. It is reading the 32 Byte memory as well. These 40 Bytes are used to identify a Figurine towards the Boxine Cloud.
There is no cloning possible as of now because all the magic tags that are known to me are within the SLIX standard. These are lacking of the privacy mode and do have to much memory on board. Both features are checked within the Toniebox firmware. That means you would be able to make a tag that has the same UID and the first 32 Byte will have the same content than the original Tonie figurine Tag has, but the Box will still refuse to work with this tag.
The proxmark3 is capable to read the full content of the Tonie figurine Tag if this is not in privacy mode. The isceman and the original firmware are not able to disable the privacy mode. Therefor you could either the Knock-Methode I discovered and described in another post in detail or you coud use the Team RevvoX firmware for the proxmark3 where some features to handle the original Tonie Tags are added. This firmware supports some additional features of TeddyBench as well.
Hope I could help you a bit.
Regards,
Gambrius
P.S.: If anyone has a magic tag within the SLIX-L standard, please get in touch with me.
„it can simulate the Tonie rfid chip as well (more to this in another post)“ – do you have any more information on emulating the chip using a Chamelon mini? Mine is collecting dust and this would be something to play around with 😉 Last time I (briefly) tried it, I was not able to read the tag, let alone clone it. (However, I did not play around much with different firmware versions).
Hallo Matt,
We did not develope anything for the ChameleonMini because there are to many HW Versions out there that are not compatible to each other.
Therefore we concentrated on the Proxmark3 easy, where the FW development goes parallel to all HW revisons
G3gg0 (Teammember of RevvoX) came up with a modified version of the original Proxmark3 FW which is able to read and simulate a tonie figurine.
I will come up with a post about the simulating tonies, but this will take a bit more time, because this is not the main priority.
Regarding ChameleonMini: There is a 3C36 talk out there where they show how to emulate the UID of a tonie. This leads to the possibility of starting the audio on the Toniebox, but therefore it must already be downloaded with the original tonie figurine. a complete simulation was not possible with their solution.
Regards,
Gambrius
Hallo 🙂
toller Blog, lese mich gerade ein.
Eine Frage zu den Chips, diese hier gehen nicht, oder:
https://www.ebay.de/itm/363228072465?hash=item5492148a11:g:~HYAAOSw8DNf31lr
Ich finde nirgendwo Chips in dieser „Ampullen-Form“ wie die in den Toniefiguren.
Danke für deine Antwort/Hilfe.
Viele Grüße
ENF
Hallo ENF,
Der von Dir genannte Link ist in Ordnung. RFIDfriend verkauft sowohl über eBay, als auch über eBay Kleinanzeigen. Er hat definitive die original NXP ICODE SLIX-L Tags die mit der Toniebox funktionieren.
Die om Tonie vorhandenen NFC Tags sind Sonderformen, die auch nicht dem korrekten Antennen Standard enrsprechen. Der Empfang der Im Tonie verwendeten Tags ist sehr begrenzt und rein für die Toniebox abgestimmt. Deshalb kann man diese auch leider so nicht kaufen. Aber die Klebetags von RFIDfriend haben ausser der ringförmigen Antenne genau den gleichen NXP Chip verbaut.
Gruß,
Gambrius
Hallo zusammen,
ich bin auch gerade dabei mich mit dem Chameleonmini reve rebooted einzuarbeiten…
Die Tags, die ihr bei eBay gefunden habt, kann man da die letzten Bytes der UID frei programmieren? Das wird nicht erwähnt. Oder sind die immer fest?
Gruß
Olli
Hallo Olli,
für die SLIX-L Version sind aktuell keine china magic tags bekannt. Heisst also, dass diese immer eine eindeutig gesetzte UID haben (da original NXP Chip). Diese kann nicht verändert werden.
Bei den Tags die bei eBay angeboten werden (https://www.ebay-kleinanzeigen.de/s-anzeige/original-nxp-icode-slix-l-rfid-tag/1358523486-168-3480) handelt es sich um original NXP Chips. Die kann ich für die Verwendung auf jeden Fall empfehlen.
Passt auf und lasst Euch keine „kompatiblen“ Chips anbieten. Hierbei handelt es sich um China fakes (kein MAGIC!!). Die Chin fake chips fallen nach ein paar mal Benutzung aus.
Gruß,
Gambrius
Hallo,
besteht denn die Möglichkeit einen bereits vorhandenen Tonie auf einen leeren SLIX-L zu klonen? Ich würde gerne besser greifbare Holzfiguren für unsere kleine nutzen.
Hallo Micha,
auf Deine Frage kann ich ein klares JEIN geben.
Ein Klone des original Tonie Chips ist nicht möglich, da zum einen der Chip-Standard bereits aussagt, dass dieser eine UID (unique identifier), also eine eindeutige / NUR einmal vergebene Seriennummer besitzt.
Es gibt zwar so genannte Magic Tags, chinesische fake chips, bei denen man die UID beliebig verändern kann. Jedoch ist mir bis jetzt keine changeable UID für den sehr spezifischen SLIX-L Chip bekannt.
Es ist jedoch möglich, den bereits auf der Toniebox befindliche Audioinhalt einem neuen Tag zuzuordnen. Wenn dieser mit einer original Toniefigur herunter geladen wurde, kann dieser dann anhand der UID des custom tags neu verlinkt werden. Sobald dann der custom tag aufgelegt wird, wird der gleiche Inhalt abgespielt, der auch bei dem original Tonie abgespielt werden würde. Hierbei ist jedoch zu beachten, dass die Box beim Verwenden der custom tags im Offline Modus laufen muss, da ansonsten das Audiofile gelöscht wird. Also nur in den Online Modus wechseln, um die Audioinhalte anhand der original Tonies zu laden. Ansonsten dioe Box im Offline Modus betreiben.
Gruß,
Gambrius
Lots of excellent info here.
I have a question… I placed a creative Tonie on my box, but before I could load content, the dog ate it, and the chip is broken. So, if I were to inspect the SD card, it would have the UID of this figure? Does that mean I can get a new SLIX-L chip and give it the same UID, and then I can continue using this new chip within Boxine cloud?
Hallo,
Unfortunatelly you can not use it within the cloud anymore.
Because you are not able to change the UID of the tag, but the reference UID to the audio on the sd card.
Ao if you get a custom rfid tag, you could use the UID of this tag and link your already downloaded content on your sd card to this custom tag. This way you can play the audio.
Regatds,
Gambrius
Question? Do you have the dimensions of the actual rfid chip you removed? I am printing a figurine to try and am planning on just cutting open a creative tonie for the chip vs copying my own. But I need the length to leave a slot open for it and I haven’t received the tonie I am harvesting from yet
Sorry, I do not have the actual dimensions of the Chip.
But I would rather go with a custom NFC Tag like the ones from RFIDfriend than cutting a Tonie figurine a part.
Hi,
is it possible to emulate a tag with an ESP8266 and a PN5180 RFID reader?
The reader documentation says yes, but I cannot find anything in the ATrappmann library.
Thanks in advance!
Hallo,
Emulation of a Tonie tag with the PN5180 is NOT possible.
Tonie Tags are based on ISO15693. The PN5180 can only emulate ISO144443 tags.
But you can use a proxmark3 or Flipper zero. Both are able to emulate a Tonie Tag if you use the modified firmware we (Team RevvoX) prepared for these.
Regards,
Gambrius
Hi,
many thanks for your content.
Is ist possible to emulate a tag with an ESP8266 and a PN5180? Reading and writing seems to be no problem with the ATrappmann library but i can’t find anything to emulate a tag.
Many thanks in advance.
Hallo,
Emulation of a Tonie tag with the PN5180 is NOT possible.
Tonie Tags are based on ISO15693. The PN5180 can only emulate ISO144443 tags.
But you can use a proxmark3 or Flipper zero. Both are able to emulate a Tonie Tag if you use the modified firmware we (Team RevvoX) prepared for these.
Regards,
Gambrius